iGPT vs Threat Watch
Side-by-side comparison to help you choose the right tool.
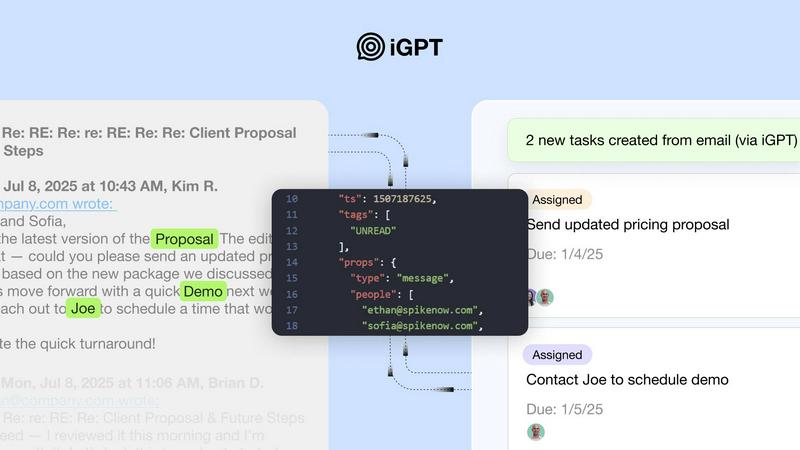
iGPT instantly gives AI agents trusted context from messy email data.
Last updated: March 1, 2026
Threat Watch
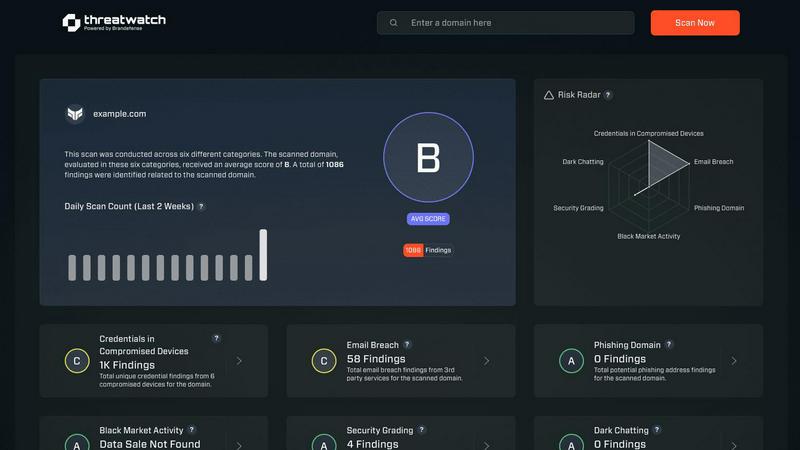
Threat Watch instantly reveals your cybersecurity health by scanning for compromised accounts and dark web threats.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Intelligence Endpoint
This is iGPT's killer feature. Instead of managing a complex pipeline of vector databases, chunking logic, and multi-step prompt chains, you send one natural language request. The API handles retrieval, context shaping, and reasoning in a single, elegant pipeline, returning responses ready for automation in ~200ms. It’s a developer experience masterpiece that replaces weeks of integration work with a single curl command.
Deep Email & Attachment Processing
iGPT doesn't just skim subject lines. It deeply indexes entire email conversations, automatically reconstructing threads across time and participants. More impressively, it processes attachments—PDFs, spreadsheets, documents—extracting text, data, and structure to understand the full context of a conversation. This holistic view is what separates real intelligence from simple keyword matching.
Enterprise-Grade Security & Compliance
In a world rightfully paranoid about data leaks, iGPT's security model is a standout. It operates on a zero data retention policy, processing each inference in memory without storing inputs, prompts, or outputs. Combined with OAuth-only processing, granular Role-Based Access Control (RBAC), and a full audit trail, it allows enterprises to leverage powerful AI without the compliance nightmare.
Context Engineering Framework (CEF)
This is the secret sauce behind the quality of responses. iGPT's CEF automatically optimizes context windows for your LLM, applying hybrid retrieval (semantic + keyword + filters) that is scored and reranked in one call. It delivers cited answers linked directly back to source emails and files, providing not just an answer but the verifiable evidence behind it, eliminating the need for manual prompt tuning.
Threat Watch
Comprehensive Cyber Health Score
This is your north star. Threat Watch doesn't just dump data on you; it synthesizes findings from compromised credentials, devices, phishing, and dark web exposure into a single, understandable health score. This immediate grade is invaluable for benchmarking your posture, tracking improvements over time, and communicating risk to non-technical stakeholders. It turns complex threat data into a clear, actionable metric.
Real-Time Dark Web Surveillance
This is the feature that often delivers the biggest "oh no" moments—and that's a good thing. Threat Watch continuously monitors underground forums, marketplaces, and leak sites for your organization's data. If employee emails, company passwords, or internal documents appear for sale, you're alerted immediately. This proactive surveillance is critical for containing breaches before they're exploited at scale.
Compromised Credential Detection
Relying on employees to know they've been pwned is a losing strategy. Threat Watch automates this by cross-referencing your corporate email domains against vast databases of known breaches. It instantly identifies which employee accounts have leaked passwords, allowing your IT team to enforce resets before those credentials can be used in a targeted attack.
Phishing & Impersonation Monitoring
Beyond data breaches, Threat Watch scours the internet for phishing kits and fake domains impersonating your brand. It looks for suspicious sites using your company's name, logos, or similar URLs designed to trick customers or employees. Discovering these campaigns early allows you to take them down swiftly, protecting your brand's reputation and your users.
Use Cases
iGPT
Autonomous Email Assistants
Build agents that do more than just draft replies. With full conversational and attachment context, these assistants can prioritize inboxes, summarize critical threads, suggest actions, and even auto-generate tasks or calendar invites—all while understanding the nuanced history and relationships between participants.
Customer Support Copilots
Revolutionize support by instantly rebuilding a customer's entire story. iGPT can analyze long, messy email chains, track tone shifts, and cross-reference attached documents (like invoices or error logs) to give support agents a complete, chronological history in seconds, drastically reducing resolution time and improving customer satisfaction.
Workflow & CRM Automation
Automatically extract decisive momentum from communication chaos. Transform email threads into structured tasks, approvals, deadlines, and CRM updates. Flag stalled deals or pending decisions by analyzing communication patterns and extracting key details like owners, dates, and commitments directly from the conversation.
Compliance & Audit Trail Generation
For regulated industries, iGPT is a game-changer. It creates a verifiable, citable audit trail by tracing feedback, approvals, contractual terms, and operational rationale directly back to the original email and attachment source. This turns unstructured inboxes into a searchable, compliant record of decision-making.
Threat Watch
Proactive Risk Management for IT Teams
Instead of waiting for a breach to happen, IT and security teams can use Threat Watch as their daily briefing. The platform prioritizes risks, allowing them to focus on resetting compromised accounts, isolating infected devices, and issuing phishing warnings before a major incident occurs. It transforms their role from reactive firefighting to strategic defense.
Executive & Board-Level Reporting
For leaders who need to understand cyber risk without technical jargon, the Cyber Health Score and clear category breakdowns are perfect. A CISO can use Threat Watch reports to visually demonstrate the organization's exposure, justify security budget requests, and show tangible improvement over time, building crucial boardroom confidence.
Due Diligence for Mergers & Acquisitions
Before acquiring or merging with another company, you need to know what you're buying into. Threat Watch can provide a rapid assessment of the target company's exposed credentials, dark web presence, and phishing risk. This cybersecurity due diligence can reveal hidden liabilities and inform negotiation or integration strategies.
Enhanced Security Posture for Remote Workforces
With employees using personal devices and accessing corporate data from everywhere, the attack surface has exploded. Threat Watch helps identify compromised personal emails linked to work accounts and malicious software on remote devices, providing essential visibility for securing a distributed workforce.
Overview
About iGPT
In the chaotic world of enterprise software, email remains the final frontier—a messy, unstructured battleground where most AI tools spectacularly fail. iGPT is the definitive, purpose-built solution to this problem. It's not just another API wrapper; it's an intelligence layer that transforms the raw, nuanced data of email threads and attachments into structured, actionable, and trustworthy context for AI agents and automated workflows. Think of it as the critical middleware that finally allows your systems to understand the human conversations where real business decisions are made. Its core proposition is breathtakingly simple: a single, unified API call that obliterates the entire fragile, labor-intensive stack of parsing, chunking, indexing, and endless prompt engineering typically required to work with email. Built with uncompromising enterprise-grade security—featuring zero data retention, full audit trails, and granular RBAC—iGPT empowers developers to deploy confident, context-aware agents for sales, support, and operations without ever sacrificing compliance or control. If you're serious about building the next generation of autonomous workflows, this is the non-negotiable tool you've been waiting for.
About Threat Watch
Let's cut through the noise: in today's digital jungle, feeling secure is an illusion unless you have the right intelligence. That's where Threat Watch comes in, and frankly, it's one of the most straightforward and actionable cybersecurity health dashboards I've seen for businesses. This isn't just another alarmist scanner; it's a curated intelligence platform designed to give you a clear, real-time snapshot of your most critical exposures. The core genius of Threat Watch is its focus on the tangible threats that actually cause breaches: compromised employee credentials, hijacked devices, phishing traps, and your data being traded on the dark web. It meticulously analyzes your organization's digital footprint across these key categories, delivering what I like to call a "cyber vital signs" report. It's built for proactive leaders—from the resource-strapped startup founder to the enterprise CISO—who are tired of operating in the dark and need prioritized insights, not just raw data. The main value proposition is undeniable: speed and clarity. You get automated, continuous assessments that tell you exactly what's wrong and, by implication, where to direct your team's efforts first. If you believe that prevention is infinitely cheaper than reaction, Threat Watch provides the foundational intelligence to make that possible.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is architected for the enterprise with a foundational commitment to privacy. It employs a strict zero data retention policy, meaning your emails, prompts, and outputs are never stored post-processing. All inferences run in memory. It uses OAuth for authentication and enforces granular Role-Based Access Control (RBAC) on every request. Furthermore, your data is never used to train or improve any models.
What makes iGPT different from using a generic LLM API on email text?
A generic LLM API sees raw, messy text. iGPT provides deep, structured context. It automatically reconstructs email threads, processes attachments, and uses its Context Engineering Framework (CEF) to perform hybrid retrieval and optimal context shaping before the LLM even sees the query. This results in faster, more accurate, and fully cited answers without you building and maintaining a complex retrieval pipeline.
What types of email sources and attachments can it connect to?
iGPT is designed to connect to standard enterprise email sources. It deeply indexes emails from connected accounts. For attachments, it has robust processing capabilities for common business documents including PDFs, Word documents, Excel spreadsheets, and PowerPoint presentations, extracting both text and structural data to inform its understanding.
Is there a way to test iGPT before committing?
Absolutely. iGPT offers a comprehensive live playground where you can connect test data sources, experiment with different CEF quality tiers, and make real API calls to see the results. They even provide $10 in free credits to get started, with no credit card required, which is a fantastic and low-risk way to evaluate its power firsthand.
Threat Watch FAQ
How does the free scan work?
The free scan is a brilliant, no-commitment way to see the power of the platform. You simply provide your company's primary domain name (e.g., yourcompany.com). Threat Watch then performs a non-intrusive scan of its databases and monitoring sources for compromised credentials, dark web mentions, and phishing sites associated with that domain. You get an immediate snapshot of your exposed surface area without needing to install any software.
What kind of alerts will I receive?
You'll receive prioritized, actionable alerts, not noise. These include specific notifications when employee credentials are found in a new data breach, when your company is mentioned on a dark web forum, when a new phishing domain targeting your brand is registered, and if company-owned IP addresses are associated with malware infections. Each alert includes context and recommended steps.
Is Threat Watch suitable for a small business without a dedicated IT person?
Absolutely, and this is one of its strongest suits. The interface is designed for clarity, not complexity. The health score and categorized results make it easy for a business owner or office manager to understand the top risks. For very small teams, even just using it to identify and reset compromised employee passwords is a massive security win.
How is this different from my antivirus software?
Antivirus software is a vital internal guard—it tries to stop malware already on a device. Threat Watch is an external intelligence service. It looks for threats outside your walls: stolen data on the internet, phishing campaigns, and discussions about your company on the dark web. They are complementary layers; one protects the endpoint, the other gives you strategic warning about incoming attacks.
Alternatives
iGPT Alternatives
iGPT is a specialized business intelligence tool designed to solve a very specific enterprise problem: giving AI agents structured, secure context from messy email data. It acts as an intelligence layer, transforming chaotic email threads and attachments into actionable insights for automated workflows. Users often look for alternatives for a few key reasons. Budget is a primary driver, as specialized enterprise tools command a premium. Others might seek a broader platform that bundles email parsing with other functions, or they may have simpler needs that don't require iGPT's deep, security-first architecture for complex agentic systems. When evaluating any alternative, focus on its core competency with unstructured email data. Can it truly understand threaded conversations and attachment contents in real-time? Crucially, scrutinize its security posture and data handling policies. The best tool is one that delivers reliable context without becoming a compliance liability.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence platform that falls squarely into the business intelligence category, transforming raw threat data into a clear picture of your organization's digital health. It's designed to give you actionable insights on compromised accounts and vulnerabilities in real-time. Users often seek alternatives for a variety of practical reasons. Perhaps the pricing model doesn't align with their budget, they need deeper integration with a specific tech stack, or they require a feature set tailored to a niche compliance framework. The search for the right tool is less about finding a "better" product and more about finding the right fit for your specific operational and financial landscape. When evaluating alternatives, focus on the core value: actionable intelligence. Look beyond flashy dashboards and ask if the tool provides clear, prioritized steps to improve your security posture. Consider the quality of data sources, the automation of routine assessments, and the platform's ability to grow with your business without becoming a management burden itself.