Karolium vs Threat Watch
Side-by-side comparison to help you choose the right tool.
Karolium is a zero-code platform that empowers businesses to create AI-driven solutions quickly and easily.
Last updated: February 28, 2026
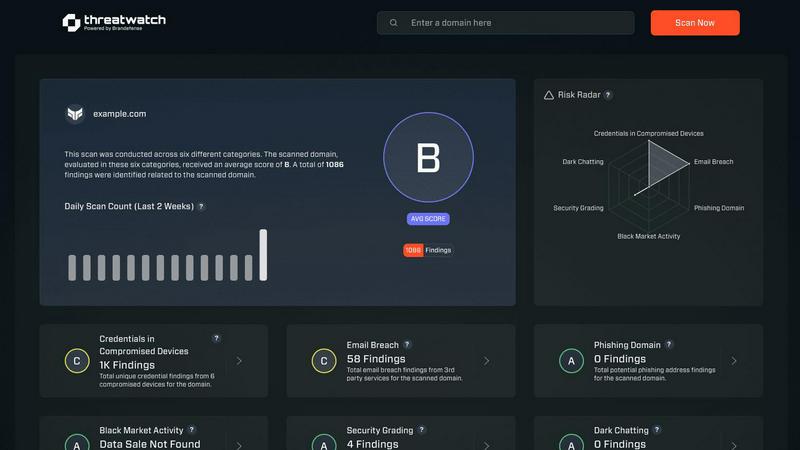
Threat Watch
Threat Watch instantly reveals your cybersecurity health by scanning for compromised accounts and dark web threats.
Last updated: March 1, 2026
Visual Comparison
Karolium

Threat Watch
Feature Comparison
Karolium
Zero-Code Customization
Karolium's standout feature is its zero-code customization capability, allowing users to build and modify applications without writing a single line of code. This empowers non-technical users to create tailored solutions that align perfectly with their business processes, significantly reducing development time.
Pre-Composed Modules
The platform offers a robust selection of pre-composed modules that can be easily deployed and customized. These modules facilitate the rapid enhancement of existing applications and the creation of new workflows, enabling organizations to adapt quickly to changing business needs.
AI Integration
Karolium seamlessly integrates AI capabilities into its platform, providing businesses with predictive and prescriptive insights. This feature allows organizations to leverage data-driven decision-making and anticipate trends, ultimately enhancing operational efficiency and strategic planning.
Managed SaaS Platform
Delivered as a managed Software as a Service (SaaS) platform, Karolium ensures continuous access to the latest technology advancements and regular updates. This feature guarantees that organizations benefit from cutting-edge capabilities without the burden of maintaining infrastructure or software upgrades.
Threat Watch
Comprehensive Cyber Health Score
This is your north star. Threat Watch doesn't just dump data on you; it synthesizes findings from compromised credentials, devices, phishing, and dark web exposure into a single, understandable health score. This immediate grade is invaluable for benchmarking your posture, tracking improvements over time, and communicating risk to non-technical stakeholders. It turns complex threat data into a clear, actionable metric.
Real-Time Dark Web Surveillance
This is the feature that often delivers the biggest "oh no" moments—and that's a good thing. Threat Watch continuously monitors underground forums, marketplaces, and leak sites for your organization's data. If employee emails, company passwords, or internal documents appear for sale, you're alerted immediately. This proactive surveillance is critical for containing breaches before they're exploited at scale.
Compromised Credential Detection
Relying on employees to know they've been pwned is a losing strategy. Threat Watch automates this by cross-referencing your corporate email domains against vast databases of known breaches. It instantly identifies which employee accounts have leaked passwords, allowing your IT team to enforce resets before those credentials can be used in a targeted attack.
Phishing & Impersonation Monitoring
Beyond data breaches, Threat Watch scours the internet for phishing kits and fake domains impersonating your brand. It looks for suspicious sites using your company's name, logos, or similar URLs designed to trick customers or employees. Discovering these campaigns early allows you to take them down swiftly, protecting your brand's reputation and your users.
Use Cases
Karolium
Rapid Application Development
Organizations can utilize Karolium to quickly develop and deploy custom applications tailored to their unique workflows. This accelerates the overall development process, enabling companies to respond swiftly to market demands and operational challenges.
Enhancing Legacy Systems
Karolium can be employed to augment existing legacy systems, allowing businesses to connect various applications and extend their functionality without undergoing a complete overhaul. This feature preserves investments in current technologies while boosting their capabilities.
AI-Driven Business Insights
Companies can harness the platform's AI capabilities to gain actionable insights from their data. With predictive analytics, organizations can identify trends and make proactive decisions, leading to improved business outcomes and strategic initiatives.
Streamlining Supply Chain Management
Karolium supports the optimization of supply chain processes by facilitating real-time collaboration among suppliers and stakeholders. Its modules for procurement, compliance, and asset monitoring enhance efficiency and responsiveness across the supply chain.
Threat Watch
Proactive Risk Management for IT Teams
Instead of waiting for a breach to happen, IT and security teams can use Threat Watch as their daily briefing. The platform prioritizes risks, allowing them to focus on resetting compromised accounts, isolating infected devices, and issuing phishing warnings before a major incident occurs. It transforms their role from reactive firefighting to strategic defense.
Executive & Board-Level Reporting
For leaders who need to understand cyber risk without technical jargon, the Cyber Health Score and clear category breakdowns are perfect. A CISO can use Threat Watch reports to visually demonstrate the organization's exposure, justify security budget requests, and show tangible improvement over time, building crucial boardroom confidence.
Due Diligence for Mergers & Acquisitions
Before acquiring or merging with another company, you need to know what you're buying into. Threat Watch can provide a rapid assessment of the target company's exposed credentials, dark web presence, and phishing risk. This cybersecurity due diligence can reveal hidden liabilities and inform negotiation or integration strategies.
Enhanced Security Posture for Remote Workforces
With employees using personal devices and accessing corporate data from everywhere, the attack surface has exploded. Threat Watch helps identify compromised personal emails linked to work accounts and malicious software on remote devices, providing essential visibility for securing a distributed workforce.
Overview
About Karolium
Karolium is an innovative unified zero-code platform designed specifically for businesses seeking to enhance their operational agility and efficiency. This cutting-edge solution enables organizations to rapidly customize applications without traditional coding, making it an ideal choice for those frustrated by the limitations of off-the-shelf software. Karolium combines the capabilities of Integration Platform as a Service (iPaaS), Application Platform as a Service (aPaaS), Operations Platform as a Service (oPaaS), and AI Platform as a Service (AIPaaS) to deliver a comprehensive solution for building, extending, and optimizing intelligent business applications. With a library of ready-to-deploy modules, users can create tailored workflows that seamlessly integrate with existing systems, driving digital transformation and operational excellence. The platform's predictive and prescriptive capabilities empower organizations to make informed decisions and leverage AI to enhance their business functions, ensuring they stay competitive in a rapidly evolving market.
About Threat Watch
Let's cut through the noise: in today's digital jungle, feeling secure is an illusion unless you have the right intelligence. That's where Threat Watch comes in, and frankly, it's one of the most straightforward and actionable cybersecurity health dashboards I've seen for businesses. This isn't just another alarmist scanner; it's a curated intelligence platform designed to give you a clear, real-time snapshot of your most critical exposures. The core genius of Threat Watch is its focus on the tangible threats that actually cause breaches: compromised employee credentials, hijacked devices, phishing traps, and your data being traded on the dark web. It meticulously analyzes your organization's digital footprint across these key categories, delivering what I like to call a "cyber vital signs" report. It's built for proactive leaders—from the resource-strapped startup founder to the enterprise CISO—who are tired of operating in the dark and need prioritized insights, not just raw data. The main value proposition is undeniable: speed and clarity. You get automated, continuous assessments that tell you exactly what's wrong and, by implication, where to direct your team's efforts first. If you believe that prevention is infinitely cheaper than reaction, Threat Watch provides the foundational intelligence to make that possible.
Frequently Asked Questions
Karolium FAQ
What types of businesses can benefit from using Karolium?
Karolium is designed for a wide range of organizations, particularly those looking to enhance operational agility and streamline application development without traditional coding. It is ideal for enterprises seeking to leverage AI and improve their existing software ecosystems.
How does Karolium support AI integration?
Karolium provides built-in AI capabilities that facilitate the creation of intelligent applications. Users can access predictive and prescriptive analytics, allowing them to make data-driven decisions and optimize business processes.
Can Karolium be used with existing software systems?
Yes, Karolium is designed to integrate seamlessly with existing software systems. Its modular architecture allows organizations to enhance and extend their current applications without the need for significant redevelopment.
What is the advantage of using a managed SaaS platform like Karolium?
Using a managed SaaS platform like Karolium offers continuous access to the latest features and updates without the need for manual maintenance or upgrades. This ensures that businesses can focus on their core operations while benefiting from cutting-edge technology.
Threat Watch FAQ
How does the free scan work?
The free scan is a brilliant, no-commitment way to see the power of the platform. You simply provide your company's primary domain name (e.g., yourcompany.com). Threat Watch then performs a non-intrusive scan of its databases and monitoring sources for compromised credentials, dark web mentions, and phishing sites associated with that domain. You get an immediate snapshot of your exposed surface area without needing to install any software.
What kind of alerts will I receive?
You'll receive prioritized, actionable alerts, not noise. These include specific notifications when employee credentials are found in a new data breach, when your company is mentioned on a dark web forum, when a new phishing domain targeting your brand is registered, and if company-owned IP addresses are associated with malware infections. Each alert includes context and recommended steps.
Is Threat Watch suitable for a small business without a dedicated IT person?
Absolutely, and this is one of its strongest suits. The interface is designed for clarity, not complexity. The health score and categorized results make it easy for a business owner or office manager to understand the top risks. For very small teams, even just using it to identify and reset compromised employee passwords is a massive security win.
How is this different from my antivirus software?
Antivirus software is a vital internal guard—it tries to stop malware already on a device. Threat Watch is an external intelligence service. It looks for threats outside your walls: stolen data on the internet, phishing campaigns, and discussions about your company on the dark web. They are complementary layers; one protects the endpoint, the other gives you strategic warning about incoming attacks.
Alternatives
Karolium Alternatives
Karolium is a cutting-edge zero-code platform designed to facilitate rapid digital transformation by enabling businesses to customize applications without the complexities of traditional coding. This platform caters to organizations seeking agility and efficiency, providing a range of ready-to-deploy modules that enhance existing applications and streamline the creation of new solutions. As businesses evolve, users often seek alternatives to Karolium due to various factors such as pricing concerns, specific feature requirements, or the need for a platform that aligns better with their unique workflows and operational structures. When looking for an alternative, it’s essential to consider factors like ease of use, integration capabilities, and the range of features offered. A robust solution should not only allow for zero-code customization but also provide advanced analytics and seamless integration with existing systems. Additionally, evaluating customer support and the scalability of the platform can significantly impact long-term satisfaction and effectiveness in meeting business goals.
Threat Watch Alternatives
Threat Watch is a cybersecurity intelligence platform that falls squarely into the business intelligence category, transforming raw threat data into a clear picture of your organization's digital health. It's designed to give you actionable insights on compromised accounts and vulnerabilities in real-time. Users often seek alternatives for a variety of practical reasons. Perhaps the pricing model doesn't align with their budget, they need deeper integration with a specific tech stack, or they require a feature set tailored to a niche compliance framework. The search for the right tool is less about finding a "better" product and more about finding the right fit for your specific operational and financial landscape. When evaluating alternatives, focus on the core value: actionable intelligence. Look beyond flashy dashboards and ask if the tool provides clear, prioritized steps to improve your security posture. Consider the quality of data sources, the automation of routine assessments, and the platform's ability to grow with your business without becoming a management burden itself.